General Data Protection Regulation (GDPR) together with the growing number of data breaches are the most pressing reasons why small and medium businesses are implementing data protection technologies – including encryption.
However, with limited time and the market flooded by various products, it can be a difficult task for companies’ owners and decision-makers to find the right fit for their needs.
If you are faced with the decision yourself, avoid pitfalls in selecting an encryption product by asking the following questions:
Which laptops present the greater risk: On-site or off-site?
This might seem like a pointless question with an obvious answer; systems are more liable to theft when away from the office. But making this distinction and keeping it in mind is the right place to start and when you have settled on a solution, be sure to test its effectiveness at managing problem scenarios for your remote users.
Does the encryption system suit the needs of your IT department for full remote control of off-site endpoint encryption?
“ALL MAJOR ENDPOINT ENCRYPTION PRODUCTS OFFER THE MEANS TO MANAGE REMOTE SYSTEMS, BUT LOOK CAREFULLY AT THE REQUIREMENTS.”
All major endpoint encryption products offer the means to manage remote systems, but look carefully at the requirements. Most need either an open incoming connection to a demilitarized zone (DMZ) on your server, or a VPN connection. All involve a higher level of IT skills that can add additional costs and, in order to function, may require the user to initiate the connection; not much use with a rogue employee or stolen laptop.
A well-designed product will give you the remote management necessary without creating additional security problems, requiring specialist knowledge, or adding expense to the project.
Why is this important?
Being able quickly to vary security policy, encryption keys, features and operation of endpoint encryption remotely, means that your default policy can be strong and tight. Exceptions can be made only when and where they are needed, and reverted just as easily. If you can’t do this you’ll be forced to leave ‘a key under the doormat’, just in case — tearing holes in your policy before deployment is complete.
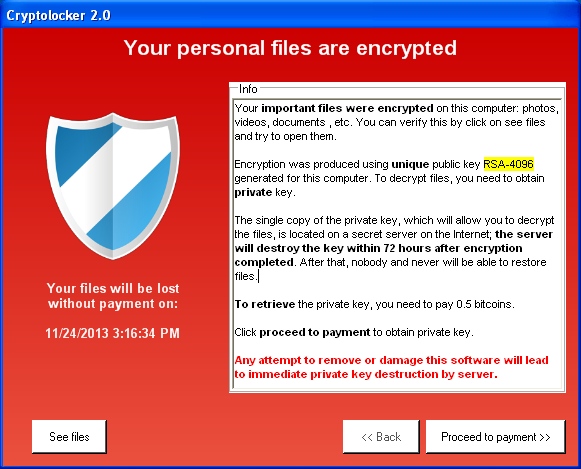
Does the solution allow remote locking and wiping of keys from laptops?
The answer might be crucial if a company computer with full-disk encryption gets stolen while in sleep mode or with the operating system booted up. It’s even worse if those systems come with the pre-boot password affixed on a label or tucked in the laptop bag. If a remote lock or wipe function is not available, then the system is either unprotected or secured only by the OS password, with the encryption being bypassed in either case.
Similarly, it is important to know whether the solution has been designed to accommodate the typical use cases that would otherwise unravel a well designed security policy.
Does the solution secure removable media without having to whitelist each item?
With an array of writeable devices that people use for their everyday work, it is almost impossible for the admins to whitelist each and every one of them, and decide whether it’s permissible to read from, write to, or not access the device at all.
It is much easier to set a file-level policy – distinguishing between files that need encryption and those that don’t – and keep these protected every time they move from workstation or corporate network to any portable device.
In other words, if you connect your own USB stick, it won’t force you to encrypt your private data; anything coming from the company system, however, will be encrypted without the keys being held on your device. It is a simple idea, but one which makes any device safe, without the need for whitelisting.
Closing Remarks: The security was there a long time ago; what will make or break your deployment is flexibility and ease of use.
In the end you need to figure out if the solution you want to use is easy to deploy. If the setup of the solution takes hours or even days and needs additional tools for its operation, it might cause new headaches for company sysadmins and create new security risks. Aim for an easy-to-deploy solution that doesn’t require advanced IT expertise and preserves both finances and your human resources. If the user experience mirrors that easy deployment, then IT staff won’t be further taxed by user lockouts, lost data and other frustrations.
All validated, commercial encryption products have been more than strong enough for many years, yet a significant proportion of the recorded data breaches involving lost or stolen laptops and USB drives happened to organizations who had bought and deployed encryption products.
Reading the case notes for these incidents reveals that being able to fit the solution to your environment, working practices and making encryption easy for everyday users as the real challenges.
Source: Welivesecurity