That escalated quickly! For those of you who did not read any news on Friday (or had your heads in the sand), you need to know that a massive tidal wave of malware just struck Planet Earth, creating gigantic waves in the information security sphere and even bigger waves for the victims. The culprit? A piece of ransomware, called WannaCryptor by ESET but also going by Wanna Cry and Wcrypt, has been spreading rapidly and it is utilizing leaked NSA files, namely the eternalblue SMB exploit.
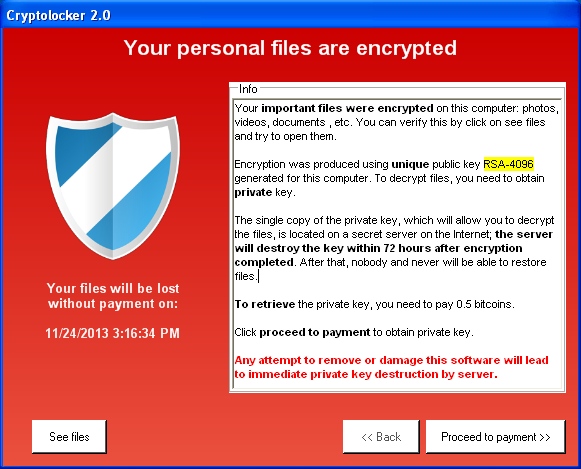
Unlike most encrypting-type malware, this one has wormlike capabilities, allowing it to spread by itself. As a result, it has spread very quickly indeed. This is what victims of the English language version see:

The story started in Spain’s telecom sector, and quickly spread from that point onward and outward. Here is a version in Italian:

Many reports of healthcare related organizations being affected then appeared, plus various commercial websites, entire enterprise sites, and just about every type of network in between.
The worst issue that is being dealt with by victims is this: the files touched by the attack are encrypted and the attacker is the only source for the key to reverse that. This can have dire consequences, especially in the healthcare sector. Encrypted patient records, doctor’s files and other items may not be usable or accessible unless there is a good backup to restore from.
The ransom demanded for decryption of the files appears to be about $300, which is actually lower than other ransomware we have seen, but the true cost will be all the time, lost files, and other collateral damage caused by this malware.
There is also another theme emerging in the wake of this outbreak: Responsibility. The exploit that is being used, eternalblue, is openly available for download from a multitude of forums. I am all for research; however, providing a well-built exploit on a public forum that can affect hundreds of thousands of active machines seems a bit much, at least from where I am sitting currently. What happened to RESPONSIBLE disclosure???
The Responsible Response
Fortunately, to protect yourself against this latest threat, there is much that you can do, and you should probably get started sooner rather than later:
- Install Anti-malware Software – You may have heard this over and over, and it seems very repetitive mentioning it now. However, if I had not encountered multiple instances where I was told, “It is a server, and we have firewalls, so I will leave anti-malware off of this machine” or “I have too many problems to install antivirus on this server”, I would not mention it. But, that has happened. So, I am stating it. Please install reputable anti-malware and give yourself a fighting chance at stopping this before you are affected.
- As an example, ESET’s network protection module was already blocking attempts to exploit the leaked vulnerability at the network level before this particular malware was even created. ESET increased the protection level by adding detection for this specific threat as Win32/Filecoder.WannaCryptor.D; first detected in the 15404 VSDs, released May-12-2017, 13:20 CEST (UTC/GMT +02:00). Prior to that, ESET LiveGrid protected against this particular attack starting around 11:26AM CEST.
- Update Your Windows Machines – Please! I know that patches can be very, very difficult to get deployed across the entire network. This one, you will want to install. It has been available since mid-April and actually stops the exploit from gaining a foothold in your environment. The patch listing for the entire listing of Equation Group files can be located here.
- Be Intelligent! – As a person who researches infections, exploits and various other information security related items, knowing is half the battle. Especially when items are being leaked and created in this kind of rapid-fire fashion. Using Threat Intelligence , I was able to create the appropriate YARA rules that identified the droppers, files and characteristics pertaining to the Equation Groups leaked exploitation files. There has been a LOT of detections of these objects. My dashboard lit up like a Christmas tree within the last few weeks, and I do not expect it to stop anytime soon. This kind of intel, and more importantly, the feeds that are provided, could help you to make better decisions on what to protect and how to protect it (as in apply MS patches, are they targeting MY business, etc.)
There is more on the WannaCryptor threat, and ESET-specific protection strategies, in this ESET Knowledge Base article. To check on the amounts that the malicious actors have received in bitcoin funds from this outrage, you can check this link.